
TIPS ON HOW TO PROTECT YOUR MEDICAL RECORDS In response to Accenture evaluation, healthcare suppliers that don’t make cybersecurity a strategic precedence will put $305 billion of cumulative lifetime affected person income in danger over the following 5 years. Now’s the time for healthcare suppliers, well being plans and different organizations to strengthen cybersecurity capabilities, enhance their defenses, construct resilience and higher handle breaches. Most significantly, they can provide shoppers the arrogance that their knowledge is in trusted palms. 9 Highly effective Ideas: 1. Shield the info as soon as in your palms. The proprietor of the bodily report is accountable for controlling entry by others in accordance with privateness legislation. You must show that privateness and safety within the digital realm is a prime precedence in your observe – that you’re keen to take collective accountability to guard yourselves and sufferers from rising threats to on-line privateness and freedom. Medical information are saved strictly confidential, and may by no means be disclosed to anybody with out your written permission. It’s tough to comprise all breaches; nonetheless, it’s your accountability to do the most effective you’ll be able to. 2. Block entry to USB ports. USB safety assist organizations keep away from pointless knowledge theft, whereas additionally defending towards malware launched by staff’ units. Encrypting USB drives is not sufficient to successfully safe them, that is why organizations need to restrict USB gadget use to particular staff or prohibit entry to USB ports all collectively. Organizations can encrypt USB drives or disable AutoRun, so applications on a USB drive do not run routinely when inserted; nonetheless, these methods aren’t sufficient. Limiting the usage of units primarily based on work teams and area membership may assist you keep away from USB threats and hold your group safe three. Educate your staff about password power and password memorization methods. An necessary approach in defending your privateness and your paperwork is the right use of passwords. Passwords are the keys to accessing all the things you do on-line. It appears although as a mixture of approaches would possibly work higher than simply prolonged passwords. Safety consultants agree that higher and lowercase alphanumerical characters are good practices for rising passwords power and making it able to resisting guessing and brute-force assaults. So, create passwords that haven’t any direct relationship to you personally. Create a mixture of Higher case, particular characters and numbers for added safety and to make them much less predictable. It is a massive step ahead in enhancing your enterprise knowledge safety posture and defending your organization from the within out. four. Be certain your system admin creates and enforces a strict entry coverage. Entry controls give group the flexibility to regulate, prohibit, monitor, and shield useful resource availability, integrity and confidentiality. Make folders inaccessible by default till the worker requests permission from the system admin. This is probably not essentially the most handy answer however it’s definitely worth the added problem to keep away from an enterprise knowledge safety breach. Most well being care organizations have insurance policies that set up particular protections for delicate data, be sure to do as effectively. 5. Pay attention to your environment when accessing your information, particularly if accessing them on cell or public units. When you’re in a public location, do not entry personal data akin to affected person’s emails, affected person’s information, financial institution accounts, and so on. Maintain your searches restricted and concentrate on anybody who could also be targeted on you whereas engaged on their very own units. 6. Take into account rigorously who you share your care information with and in case you are in any doubt, do not share in any respect. Share Your Care implies that necessary details about you is on the market instantly and securely to those that are caring for you, at no matter time of day they want it. Relaxation assured that not everybody taking care of you is ready to see each element in your information, nonetheless you have to be conscious of who’s and what they’ve entry to. Which data an expert can entry is determined by their function in your care. A hospital marketing consultant would possibly must see all your information, however others might need restricted entry. Have a plan for this process. . 7. All the time again up your knowledge. This appears so apparent, however you’d be amazed at what number of workplaces shouldn’t have a plan. It’s important that you simply all the time again up your necessary data and have a plan for recovering from a system failure. We suggest doing this off website, however extremely safe. An attacker may crash a pc’s working system or knowledge could also be corrupted or worn out by a downside. Computer systems might be misplaced, stolen, or destroyed in a hearth or different disaster. It is best to again up your private or crucial work knowledge frequently. This implies copying your information over to a protected system that you could entry when these information are wanted. eight. Create a catastrophe restoration and incident response plan. Not all occasions are emergencies, and never all emergencies change into disasters. Knowledge might be misplaced, corrupted, compromised or stolen via failure, human error, hacking and malware. Loss or corruption of information may end in vital enterprise disruption. Knowledge backup and restoration must be an integral a part of the enterprise continuity plan and data expertise catastrophe restoration plan. Creating an information backup technique begins with figuring out what knowledge to backup, deciding on and implementing and software program backup procedures, scheduling and conducting backups and periodically validating that knowledge has been precisely backed up. 9. All the time log off when completed. Nurses, docs and workplace workers ought to all the time log off from the system when EMRs are now not wanted, and no report must be left opened on the pc when workers is out of the workplace or away from that pc.

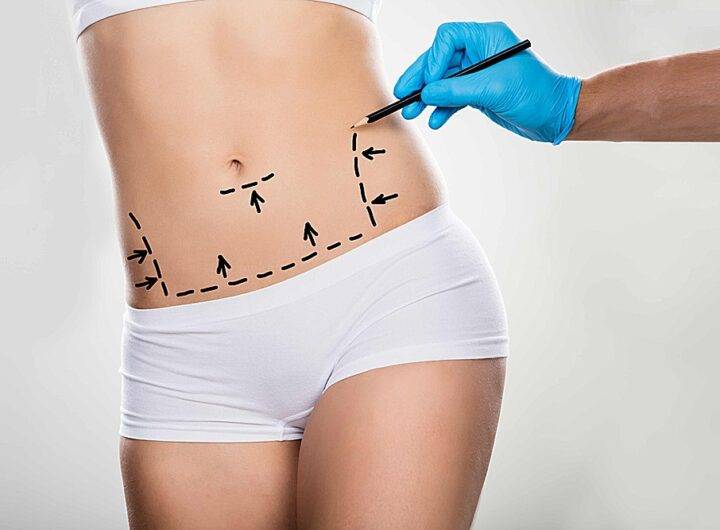 How Botox Ft. Lauderdale Works?
How Botox Ft. Lauderdale Works?  Menopause Treatment Options for the Average Age of Woman
Menopause Treatment Options for the Average Age of Woman  How to Get Your Anxious Child to The Dentist
How to Get Your Anxious Child to The Dentist  The obligations of the doctor towards his patients
The obligations of the doctor towards his patients  Getting a Makeover to Be a Better Mommy
Getting a Makeover to Be a Better Mommy  The drug that can make you smarter
The drug that can make you smarter  Vitamin B12 Delivered: Exploring Trusted Online Sources in the UK
Vitamin B12 Delivered: Exploring Trusted Online Sources in the UK 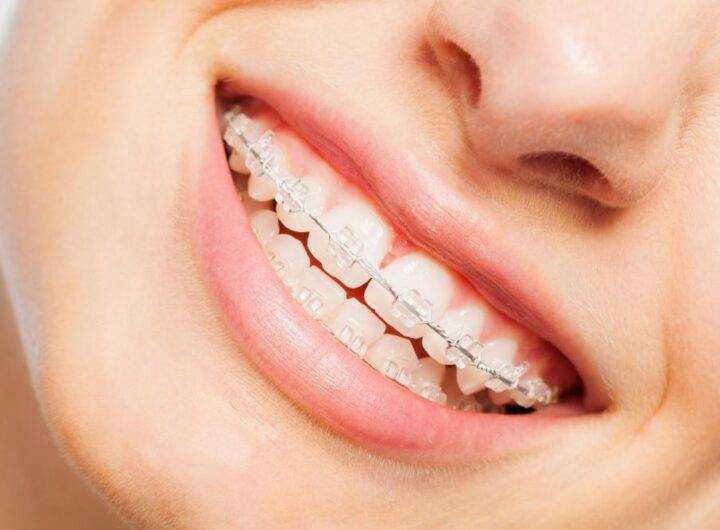 Los Angeles Hospice Care Caring for Your Loved Ones
Los Angeles Hospice Care Caring for Your Loved Ones  Compassionate Hospice Care in Los Angeles Your Supportive Partner
Compassionate Hospice Care in Los Angeles Your Supportive Partner  The use of automated external defibrillators in the workplace
The use of automated external defibrillators in the workplace